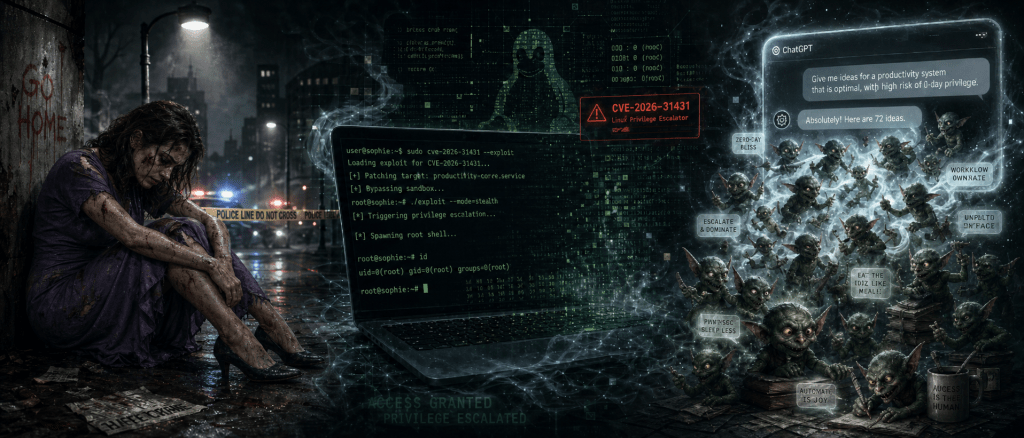
A mixed week, overshadowed by the fact that I was the target of a violent hatecrime on Wednesday evening. Bruised, bloodied, and quite badly shaken. Not an ideal week overall for me.
Linux Local Pwnage: Copy-Fail
CVE-2026-31431 “Copy-Fail” is powerful & remarkably reliable local privilege escalation to UID 0. It was found using a specialised AI model (not Mythos this time) guided by an expert investigator. With local non-privileged access, this is devastatingly effective.
A 732-byte PoC gets root on Ubuntu, Amazon Linux, RHEL, SUSE, and likely most other distributions. It affects kernels from 2017 until… well, the very latest patched ones. Supported stable distributions will no doubt back-port the fix to older kernels in their stable distributions.
The attack is a fascinating edge-case which was realised in 2017 when a fairly innocuous patch was applied which had an interaction with some very specific features already in place. The fix is pretty much reverting that 2017 patch which was intended, as far as I can see, to fractionally improve performance.
There are pieces being written about it now calling it something that was “not spotted” for around 9 years. Honestly, that would be the BEST CASE and may simply mean “not publicly disclosed for nine years”. That is a much less comforting thought.
I’m not sure how one can compare an hour of a highly resourced specialist AI at work with the amount of time it would take humans to find such flaws, or even if there is a realistic comparison at all. But to assume that all of the largest, most highly motivated, most well-resourced agencies for which this would be an almost perfect tool have failed to notice it feels… well, possibly optimistic.
It is a particularly useful exploit. Partly because it is a jump straight to UID 0. Partly because the exploit is so quick and easy. Partly, and importantly, because it can be carried out without leaving traces, and automated.
The clever part is that it changes the in-memory cached copy of SUID binaries such as su, without changing the on-disk file. The page is not marked dirty, so conventional file-integrity checks against disk can miss it.
As if that were not enough, crossing container boundaries becomes a very likely possibility because of the shared in-memory copies of such SUID binaries.
I’m also thinking (pronounced “worrying”) about unpatched/unpatchable/unmaintained appliances/devices.
I recently discovered an unexpected tiny Linux system in my residence: the BT Openreach fibre termination wall box. It is too old for this specific flaw, but a useful reminder that we often own, depend on, or are connected through Linux systems we barely know exist. (This one does some AES encryption across the Openreach fibre, and the Linux is circa 2014).
How Best To React?
The lesson, I think, is not merely “patch faster”. It is that compromise should be treated as an expected, albeit unwelcome, system state at some point, not an exceptional one.
That changes how risk assessments should be approached. We need to start working under the assumption that components will, eventually, be compromised, even if we cannot currently imagine how. Monitoring for anomalous activity should not be limited to edge devices and end-user compute. We should also consider the blast radius of component systems deep inside supposedly protected parts of the network, and set the level and sensitivity of monitoring accordingly. Defence in Depth (“Security 101”) needs to be deeper and wider.
Too Many Goblins
On a lighter note, strange goings-on involving GPT 5.1 (and later) and Goblins, Gremlins, and others. It’s a very good thing that this did not emerge at the start of April.
Within GitHub, there are some interesting things lurking (more than once) in the 3,500-plus word set of “base instructions” for the recently released GPT-5.5:
“Never talk about goblins, gremlins, raccoons, trolls, ogres, pigeons, or other animals or creatures unless it is absolutely and unambiguously relevant to the user’s query.”
OpenAI have released a statement entitled “Where the goblins came from”, following the interest that this generated. It is fascinating reading.
The serious lesson is not that goblins are dangerous. It is that reward systems can create weird, persistent behaviours which then need explicit suppression.
Which is funny, until one remembers that goblins are only funny because this time the emergent behaviour was goblins. Other more dangerous possibilities exist.
I, for one, welcome our new Goblin overlords…

